How to Use Proxies to Access Geo-Blocked Content Safely
One IP address quietly controls what shows up on your screen. Switch it, and whole collections of content suddenly become available. Keep it the same, and you may run straight into restrictions. Geo-blocking, corporate firewalls, school network filters, and ISP policies constantly influence what you can and cannot access online. In many cases, this goes unnoticed. In others, it can interfere with essential research, productivity tools, or professional platforms. When reliable access directly affects your work or academic performance, finding effective ways to restore it becomes important. The key is doing so without sacrificing connection speed, data privacy, or overall security. Let's break this down clearly and tactically.
How Proxies Unlock Restricted Online Content
A proxy acts as an intermediary between you and the internet. Instead of connecting directly to a website, your request passes through a separate server. That server presents its own IP address, not yours, which means the destination site sees the proxy's location rather than your real one.
This is powerful. If a platform restricts access by region, you can route traffic through a country where it's available. If a school or company firewall filters certain domains, a properly configured proxy can bypass those restrictions because traffic appears to originate elsewhere.
Location choice matters. If you are bypassing regional limits, select a country where the content is legitimately accessible and not heavily filtered. For example, users attempting to access globally restricted platforms often choose US or Western European IP ranges because they are broadly supported and less aggressively blocked.
Choosing the Right Type of Proxy
Not all proxies behave the same way. Pick the wrong type and you will experience slow speeds or frequent blocks.
Datacenter proxies are fast and cost-effective. They are ideal for streaming, quick access tasks, or high-volume browsing. However, some platforms detect and restrict them more easily.
ISP proxies combine datacenter infrastructure with residential IP registration. They look more authentic to detection systems while maintaining strong speed performance. If reliability and lower block rates are priorities, this is often the smarter choice.
If scalability is critical, IPv6 proxy pools offer a significantly larger address range. That translates into flexibility and reduced reuse patterns, which can lower detection risk.
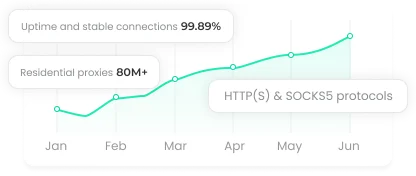
Selecting the Right Protocol
The protocol determines how your traffic is handled. This decision affects both performance and compatibility.
HTTP and HTTPS proxies are suitable for web browsing. HTTPS adds encryption, which is essential when handling logins, payment pages, or confidential material.
SOCKS5 proxies operate beyond the browser. They support torrent clients, messaging apps, and other software without altering traffic packets. If you need flexibility across applications, SOCKS5 is often the better option.
For browser-only access, HTTP or HTTPS is usually sufficient. For broader system routing, SOCKS5 gives you more control.
When a Proxy Is Not Enough
Proxies are efficient. They are also not the only tool available.
VPN services encrypt and route all device traffic through a remote server. This is ideal when you require consistent, system-wide protection and location masking.
Tor Browser routes traffic through multiple global nodes. It maximizes anonymity but sacrifices speed. Use it when privacy outweighs performance.
Mobile tethering temporarily assigns you a different IP via your cellular network. It is quick and practical for short sessions.
Public Wi-Fi networks provide a fresh IP but come with security risks. Avoid using them for sensitive accounts or confidential tasks.
If you are working in Chrome or another mainstream browser, you will need either a proxy or VPN to change your IP. Tor works as a standalone browser without manual configuration, which makes it convenient but slower.
How to Unblock Websites on School Networks
Educational institutions rely on firewalls, DNS filtering, and internal proxies to restrict entertainment or social media platforms. That makes sense in theory. In practice, legitimate research can get caught in the same net.
Here are realistic options:
A mobile hotspot is fast to deploy and bypasses internal filters entirely. It works best for short sessions where stability is less critical.
Browsers with built-in VPN functionality or Tor provide quick workarounds if you lack administrative rights to modify system settings.
Changing DNS settings can also bypass domain-level filtering. Switching to public DNS providers such as Google Public DNS at 8.8.8.8 or Cloudflare at 1.1.1.1 can restore access when filtering occurs strictly at the DNS layer. However, this will not bypass deeper firewall rules.
Android and Windows Configuration
Android allows proxy setup within Wi-Fi network settings or through dedicated proxy client apps. For workplace restrictions, Wi-Fi-level configuration is usually enough. For app-specific routing, SOCKS5 clients offer better flexibility.
Windows supports system-wide proxy configuration in Network and Internet settings. Once enabled, all browsers and many applications will route through the defined server. This approach is effective against ISP-level blocks and does not require additional software installation.
If you want the highest success rate with minimal overhead, system-level proxy configuration is often the cleanest solution.
Final Thoughts
There is no single "best" method to unblock websites. The right choice depends on your environment, your risk tolerance, and how persistent the restrictions are.
For speed and geographic targeting, proxies remain one of the most efficient tools available. For full encryption and device-wide coverage, VPNs are stronger. For anonymity above all else, Tor stands apart.
The key is intentional use. Choose the method that matches your objective, verify your IP after configuration, and prioritize security alongside access. Control your connection, and you control your reach.