How to Turn Ad Verification into a Cybersecurity Advantage
Ad fraud often hides in plain sight, quietly draining budgets and spreading malicious content. One moment an ad appears legitimate, and the next it redirects users to malware or spoofed domains. Fraud networks actively monitor traffic, block suspicious requests, and feed misleading results to verification systems they can identify, making the environment extremely hostile for cybersecurity teams. Ad verification pipelines now must operate like real users while remaining fully isolated from internal infrastructure. Any leaked patterns, session fingerprints, or exposed systems can compromise data integrity and create security risks. Effective verification requires collecting accurate, actionable insights without revealing the presence or structure of the monitoring systems.
Cybersecurity Risks Behind Ad Verification
Most ad verification systems were originally designed to collect evidence about how ads are served. Security was rarely the priority. As fraud networks grew more sophisticated, that gap became a serious weakness.
Fraud actors constantly monitor traffic patterns to identify verification tools. When they detect predictable request structures or recognizable IP ranges, they respond differently. Instead of exposing abusive behavior, they return sanitized results that appear legitimate.
This tactic completely distorts verification results. Teams think campaigns look clean, while real users are still being exposed to malicious redirects or fraudulent placements. The data may look accurate, but the underlying signals are carefully manipulated.
Even worse, verification traffic can reveal internal infrastructure. Subtle indicators like request timing, header structures, or session patterns may expose how a detection pipeline works. Over time, adversaries can learn enough to evade monitoring entirely.
Without proper isolation and realistic traffic simulation, the verification layer itself becomes a vulnerability rather than a security asset.
Infrastructure Constraints That Undermine Verification Accuracy
Verification accuracy often fails because the underlying infrastructure was never designed for adversarial environments. Several technical limitations commonly weaken verification pipelines and distort collected data.
Detectable Proxy Pools
Static or low-quality proxies are easy for fraud networks to identify and block. Once detected, they stop showing real behavior and instead serve clean responses that mislead verification systems.
IP Blocking and Fingerprinting Defenses
Ad platforms increasingly use browser fingerprinting and network detection to identify automated traffic. When verification tools trigger these defenses, the resulting ad delivery no longer reflects real user experiences.
Exposure of Internal Networks
Routing verification traffic through corporate infrastructure can unintentionally reveal details about internal systems. Attackers can observe patterns, infer tooling, and adapt their tactics accordingly.
Manual or Semi-Automated Workflows
Human-driven verification processes are slow and inconsistent. They introduce errors, reduce coverage, and make it difficult to reproduce results across campaigns.
Limited Geographic Coverage
Ads behave differently across regions. A verification system that only operates from a few locations cannot capture the full picture of how ads appear globally.
Scaling Limitations
Verification systems that cannot scale struggle to test campaigns repeatedly. That makes trend analysis, auditing, and anomaly detection much harder over time.
Weak Traffic Isolation
When verification sessions share infrastructure with production systems, both security and data integrity suffer. Fraud networks gain more visibility into how detection pipelines operate.
Each of these issues introduces blind spots. Combined, they create an environment where verification results appear clean while fraudulent behavior continues unchecked.
Swiftproxy's Cybersecurity Integration Capabilities
Swiftproxy approaches ad verification as an infrastructure challenge rather than a simple scraping task. The platform provides proxy architecture that integrates directly into cybersecurity workflows while keeping internal systems isolated.
Instead of treating proxies as disposable access points, Swiftproxy focuses on control, automation, and visibility. Security teams can run verification traffic that behaves like real user activity while maintaining strict operational separation from internal networks.
This structure allows teams to collect accurate ad delivery data without leaving identifiable traces that fraud networks can exploit.
API-First Proxy Control
Swiftproxy manages proxy operations through a fully API-driven system. Teams can control IP rotation, session management, and request routing directly through automated workflows.
Automation changes the scale at which verification becomes possible. Instead of running manual checks, engineers can integrate verification directly into detection pipelines. Repeated testing becomes simple, consistent, and far less prone to human error.
Over time, this automation creates a reliable stream of verification data that security teams can use to detect patterns and investigate anomalies.
Token Authentication and IP Whitelisting
Access to Swiftproxy's proxy network is controlled through token-based authentication and configurable IP whitelists. Only authorized systems are able to send verification traffic through the network.
This access control ensures that internal infrastructure remains protected. Even when running large-scale verification workloads, the proxy layer acts as a protective buffer between verification tasks and corporate systems.
Security teams gain the ability to scale verification operations without increasing their exposure.
Compatibility with Cybersecurity Tooling
Verification rarely exists in isolation. Security teams rely on multiple platforms including SIEM tools, scraping frameworks, and internal detection systems.
Swiftproxy integrates smoothly with these environments. Verification data can flow directly into existing threat intelligence pipelines without complex adapters or manual transfers.
This compatibility reduces operational friction and ensures that verification insights become part of broader security analysis rather than a disconnected dataset.
Automation, Scale, and Regional Targeting
Modern ad verification requires testing across different regions, networks, and environments simultaneously. Swiftproxy enables this through scalable proxy infrastructure that can handle thousands of requests across multiple locations.
Regional targeting allows teams to see exactly how ads appear to users in different countries. When automation and geographic coverage work together, verification data begins to reflect real-world ad delivery patterns rather than isolated snapshots.
The result is more accurate detection of regional fraud campaigns and localized abuse.
How Swiftproxy Enhances Ad Verification
Ad verification results are only as trustworthy as the infrastructure behind them. Swiftproxy strengthens each stage of the verification process by improving realism, reliability, and security isolation.
Safe IP Rotation
Predictable traffic patterns make verification tools easy to detect. Rotating IP addresses eliminates this problem by distributing requests across a diverse pool of connections.
Each verification request appears as independent user activity. Fraud networks are far less likely to identify the system as automated verification traffic.
This improves the ability to observe real fraud behavior instead of sanitized responses designed to fool monitoring tools.
Global Regional Diversity
Swiftproxy provides proxy coverage across 195 countries. That geographic diversity allows teams to observe ads exactly as users see them in different regions.
Regional verification often reveals discrepancies that single-location testing would miss. Ads might appear legitimate in one country while redirecting to malicious domains elsewhere.
By comparing results across locations, teams can identify patterns that expose large-scale fraud operations.
Isolation from Internal Infrastructure
Verification traffic runs entirely outside internal corporate systems. This isolation dramatically reduces the risk of exposing detection tools, internal pipelines, or sensitive infrastructure.
When verification tasks remain separated from production networks, attackers have far fewer signals to analyze. They cannot easily fingerprint the detection pipeline or infer how monitoring systems operate.
This separation protects both the verification data and the organization's internal security architecture.
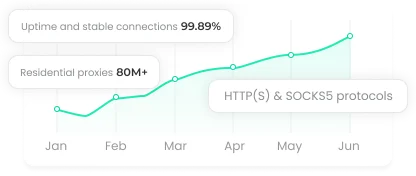
Reliable Infrastructure
Verification systems must operate consistently to produce meaningful results. Swiftproxy maintains 99.98 percent uptime, ensuring verification tasks run whenever they are needed.
Stable infrastructure allows teams to repeat tests across campaigns and time periods. Patterns become easier to identify, and anomalies stand out more clearly.
Consistency transforms ad verification from an occasional diagnostic process into a reliable component of ongoing cybersecurity monitoring.
Typical Use Cases for Cybersecurity Teams
Ad verification plays a critical role in several day-to-day security investigations. When verification infrastructure is reliable and scalable, it becomes a powerful intelligence source for identifying abuse.
Detecting Domain Spoofing Across Geographies
Domain spoofing often behaves differently depending on location. An ad may resolve correctly in one country while redirecting to a malicious domain in another.
Running verification checks from multiple geographic regions exposes these inconsistencies. Security teams can track how spoofing campaigns expand across markets before they reach larger audiences.
Comparing Mobile and Desktop Ad Delivery
Fraud networks frequently target mobile users more aggressively than desktop audiences. Desktop sessions may receive legitimate content while mobile users are redirected to low-quality or malicious pages.
Verification pipelines that simulate both environments reveal these differences. By combining proxy rotation with device-specific user agents, teams can replicate real user behavior across devices.
The resulting data highlights fraud tactics that would otherwise remain hidden.
Tracking Competitor Ad Placements Safely
Security teams sometimes analyze competitor ad placements to understand network behavior or identify risky inventory sources. Running these checks from corporate infrastructure can alter the results or trigger blocks.
Verification traffic that mimics normal user activity removes that bias. Teams gain a clearer picture of the advertising ecosystem without exposing internal networks or influencing ad delivery.
Inputting Verification Data for Threat Intelligence Analysis
Ad verification generates valuable intelligence. Redirect chains, landing pages, hosting providers, and domain infrastructure all reveal patterns of abuse.
When verification data comes from a clean and isolated environment, it can feed directly into threat intelligence models. Over time, these datasets help identify recurring domains, infrastructure clusters, and coordinated fraud campaigns.
The result is stronger proactive detection across the entire security ecosystem.
Conclusion
Swiftproxy turns ad verification into a secure, scalable, and reliable process. Teams gain accurate insights, uncover hidden fraud, and protect internal systems, making verification an integral part of ongoing cybersecurity operations and ensuring detection keeps pace with increasingly sophisticated adversaries.