What Makes a Proxy Critical for Modern Online Operations
If your business relies on the internet, and every modern business does, then your network is not just infrastructure. It is leverage. It is visibility. It is vulnerability. A proxy for business turns that vulnerability into control. This is not about hiding in the shadows. It is about operating with precision. When configured correctly, a proxy strengthens security, stabilizes performance, and gives your team the freedom to scale without tripping alarms or throttling bandwidth. That combination matters more than most leaders realize.
Why a Proxy Is Crucial
A well-implemented proxy acts as a gatekeeper between your internal systems and the open web, filtering traffic, managing requests, and shielding your infrastructure from direct exposure. That separation alone reduces your attack surface dramatically.
But protection is only one piece of the story. A proxy also lets you control how your employees use bandwidth, which applications receive priority, and how external platforms see your company online. When you manage dozens of SaaS tools, remote employees, and automated workflows, that level of control becomes crucial.
Stronger Security
A proxy masks internal IP addresses, which immediately limits direct targeting. Attackers scanning for vulnerable endpoints cannot easily map your real network structure. That alone blocks a surprising number of automated intrusion attempts.
It also allows you to filter malicious domains and suspicious traffic before it reaches employees. Instead of relying on individuals to avoid harmful sites, you enforce security at the network layer. That shifts protection from reactive to proactive.
If your team works with confidential data or external marketplaces, anonymity becomes operational insurance. Even if someone attempts active tracking, your real infrastructure stays shielded. That barrier buys time. And in cybersecurity, time is everything.
Faster Internet and Smarter Bandwidth Use
Security is important. Performance is critical. When ten employees stream training videos, download large files, and run cloud applications at the same time, your network slows. Productivity drops. Frustration rises. A proxy with caching reduces repeated external requests by storing frequently accessed resources locally.
If one employee loads a web application, the next request can be served from cache instead of the external server. That means faster response times and less bandwidth strain. The result feels simple. The impact is significant.
You can also set bandwidth rules. Limit streaming traffic. Prioritize CRM systems. Allocate guaranteed speed to revenue-critical tools. These small configuration decisions prevent network congestion before it becomes visible.
Proxy Compared to VPN
A proxy routes traffic through an intermediary server and masks IP addresses. It operates at the application or system level and focuses on control, routing, and access management. It does not typically encrypt all device traffic.
A VPN encrypts all internet traffic from the device and creates a secure tunnel to a remote server. That makes it ideal for handling financial transactions, medical data, or highly sensitive client information. The trade-off is speed and cost. Full encryption consumes resources.
If your priority is traffic management, geo-access, multi-account operations, advertising verification, or competitive research, a proxy is usually more efficient. If you require strict end-to-end encryption for every byte of data, a VPN may be necessary.
Many companies use both. They deploy proxies for operational efficiency and VPNs for specific sensitive roles.
Choosing the Right Type of Proxy
Not all proxies are built the same. Selecting the wrong type creates friction. Selecting the right one unlocks performance.
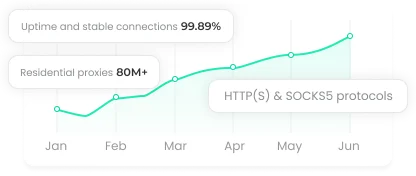
Residential Proxies
Residential proxies use IP addresses assigned to real home internet users. They carry high trust levels and blend naturally into normal web traffic patterns. That makes them ideal for web scraping, ad verification, competitor monitoring, and accessing geo-restricted resources.
They are more expensive and usually billed by traffic volume. Use them where credibility and stealth matter more than raw speed. Marketing teams and ecommerce analysts benefit the most from this category.
ISP Proxies
ISP proxies combine residential IP credibility with datacenter stability. They are hosted on servers but registered through internet service providers, which makes them difficult to flag. They are well suited for long-term sessions that require a consistent IP address.
If you need a stable identity for extended operations without sacrificing speed, this is often the sweet spot.
Common Problems and How to Solve Them
Even strong systems fail when mismanaged. Proxies are no exception.
Connection instability often results from overloaded servers or distant locations. Switch to a closer region. Upgrade bandwidth. Rotate IPs if needed. Do not accept slow performance as normal.
Blocked IP addresses usually stem from abnormal traffic patterns. Rotate addresses regularly. Use HTTPS or SOCKS5 protocols. Avoid aggressive automation that triggers detection systems.
Integration issues typically come from configuration errors. Double-check credentials. Verify port settings. Ensure firewall compatibility. When in doubt, contact the provider's technical support instead of improvising.
IP leaks are serious. Test for DNS leaks regularly. Keep software updated. Use private, reputable proxy providers rather than free public lists.
Conclusion
In short, a well-chosen proxy transforms vulnerability into control. Prioritize security, performance, and visibility, monitor usage consistently, and match the proxy type to your core business needs. Proper management ensures reliable, efficient, and scalable operations without compromising safety.