How Safe Are Proxies and When Should You Trust Them
Roughly 30% of internet users have experienced some form of data breach. That's not a niche problem. That's everyday reality. And it's exactly why tools like proxies have surged in popularity. People want privacy. Businesses want control. Everyone wants to move faster online without exposing themselves. Proxies promise all of that. But here's the catch — they can either protect you… or quietly make things worse. So, are proxies actually safe? The honest answer is simple. They can be. But only if you know what you're doing.
What a Proxy Does
Think of a proxy as a buffer between you and the internet. It sits in the middle. Every request you make goes through it first.
Instead of connecting directly to a website, your traffic is routed through the proxy server. That server uses its own IP address, not yours. Clean. Simple. Effective.
This matters more than most people realize. Your IP address reveals location, behavior patterns, and sometimes even identity clues. A proxy masks that. It adds a layer of separation that makes tracking significantly harder.
But here's where things get interesting. That same "middleman" role also means the proxy sees everything passing through it. If you trust the wrong provider, you're not protecting your data. You're handing it over.
Different Types of Proxies
The biggest divide in the proxy world isn't technical — it's trust.
Free Proxies
They look appealing. No cost. Instant access. No commitment. But there's a reason they're free. No ownership accountability.
No user vetting. No guarantees. These networks are often overcrowded, unstable, and in many cases, quietly exploited. You don't know who runs them. You don't know who else is using them. And you definitely don't know what's happening to your data in transit. That's not a small risk. That's a fundamental problem.
Paid Proxies
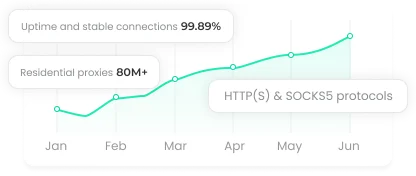
Paid providers invest in infrastructure. They monitor usage. They manage IP pools. And importantly, they have reputations to protect. That changes behavior.
You get faster speeds. More reliable connections. Cleaner IPs. But more than anything, you get accountability. That alone makes a massive difference in security.
Still, don't assume "paid" automatically means safe. Some providers cut corners. Others oversell shared resources. You need to evaluate them properly.
The Risks of Using Unreliable Proxies
Most people underestimate how risky poor proxy choices can be. The issues aren't theoretical. They're practical and common.
Poor Transparency
With unreliable proxies, you're operating blind. You don't know the source. You don't know the intent. You don't know the infrastructure. That's like routing your company's traffic through a random stranger's laptop and hoping for the best.
Malware Exposure
Some proxy networks exist specifically to exploit users. Traffic can be modified. Files can be injected. Credentials can be captured. It's not always obvious either. That's what makes it dangerous.
Information Leakage
This one is critical. Certain proxy operators log everything. Then they sell it. Browsing habits. Login details. Business data. All quietly packaged and monetized. If that information lands in the wrong hands, the damage isn't just technical. It's financial and reputational.
When Proxies Are Safe to Use
Proxies can be extremely safe when used correctly.
Choose Trusted Proxy Providers
Look for transparency. Clear ownership. Defined policies. Compliance with regulations like GDPR.
Dig into how they source IPs. Ethical sourcing isn't just a buzzword. It determines whether your usage could expose you legally or reputationally. If they can't explain their network clearly, walk away.
Getting to Know Different Types of Proxies
Residential proxies tend to be the most trusted because they route traffic through real devices. That makes them harder to detect and generally safer when sourced properly. ISP proxies can also be solid choices, but only when managed by reputable providers.
If the use case is sensitive or business-critical, go dedicated. The control is worth the extra cost.
Match the Right Proxy to the Task
This is where many people slip. For example, if you're doing web scraping, rotating residential proxies are often the safest route. They distribute requests across multiple IPs, reducing detection risk and preventing bans.
Using the wrong type doesn't just hurt performance. It increases exposure.
Lock Down Access Properly
Security isn't just about the provider. It's also about configuration. Use IP whitelisting. Use authentication credentials. Ideally both. If one layer fails, the other still protects you. It's a simple step. But it dramatically reduces the chance of unauthorized access.
Final Thoughts
Proxies can enhance privacy and perf ormance, but only when chosen and configured with care. The real difference lies in trust, transparency, and proper use. Stay selective, stay informed, and treat proxy security as part of your overall digital safety, not an afterthought.