How IP Whitelisting Protects High-Scale Proxy Workflows
A single exposed proxy endpoint can quietly become the weak link in an otherwise well-secured infrastructure. One leaked credential, one poorly restricted service, and suddenly scraping pipelines, monitoring jobs, or ad verification tools are reachable from places they should never be. The problem rarely starts dramatic. It starts small. Then it spreads. That's why IP whitelisting has become a foundational control for teams running ISP proxy services at scale. When implemented correctly, it locks proxy access to trusted systems without slowing down automation, analytics workflows, or monitoring pipelines. In this guide, we'll walk through how IP whitelisting actually works in modern infrastructures, why it breaks in poorly designed setups, and how teams can implement it without sacrificing performance or scalability.
Understanding ISP Proxies and Why Access Control Matters
ISP proxies occupy an interesting middle ground in the proxy ecosystem. They combine the trust level of residential networks with the performance characteristics of datacenter infrastructure.
Unlike rotating residential proxies that depend on peer devices, ISP proxies use static IP addresses assigned by legitimate internet providers such as AT&T, Comcast, or Cox. Those addresses are hosted on fast servers rather than household connections, which means they deliver stronger reliability and higher uptime while still appearing like genuine residential traffic.
That hybrid design creates a powerful tool for scraping, monitoring, and verification tasks. But it also introduces risk if access controls are weak. Without restrictions, anyone with credentials can potentially reach the proxy layer. That's where IP whitelisting becomes essential.
The Hidden Risks of Uncontrolled Proxy Access
Unrestricted proxy access rarely causes immediate failure. Instead, it slowly introduces security and compliance problems that grow more complicated over time.
Several issues appear repeatedly across organizations running large proxy environments.
Internal Tools Become Unintentionally Exposed
When proxy endpoints accept traffic from any source, internal services can reach them without clear boundaries. Over time, workflows expand and services begin connecting from environments that were never intended to interact with the proxy layer. The architecture becomes messy and difficult to secure.
Shared Credentials Blur Ownership
Teams often reuse the same proxy credentials across multiple services. It seems convenient at first. Then one credential leaks or someone rotates it without warning, and suddenly several pipelines fail at once. Tracing activity back to the responsible service becomes almost impossible.
Compliance Audits Lose Visibility
Security auditors want clear answers to simple questions. Which systems can access the proxy layer? Why are they allowed? When access cannot be restricted by IP address, those answers become vague. That ambiguity creates unnecessary friction during SOC 2 reviews and enterprise security assessments.
Security Reviews Reveal Unexpected Gaps
Proxy access often slips through the cracks in infrastructure diagrams. Controls exist on paper, but any machine with credentials can still reach the system. When this happens late in a review cycle, teams are forced to implement rushed fixes that disrupt production pipelines.
Why Traditional IP Whitelisting Breaks in Modern Infrastructure
On paper, IP whitelisting looks simple. Allow a few trusted IP addresses and block everything else. Real infrastructure is rarely that static. Cloud deployments, remote teams, and automated workloads constantly change where traffic originates. The result is a steady drift of source IP addresses that no longer match static allowlists.
Teams typically run into four challenges.
Controlling Large Pools of Static Proxy IPs
ISP proxies use fixed IPs rather than rotating pools. That stability is helpful, but it introduces governance problems when hundreds or thousands of addresses are shared across different teams and environments. Without clear ownership, tracking which service is responsible for which traffic becomes difficult.
Cloud Infrastructure Changing Outbound Addresses
Cloud instances frequently receive new public IPs when they restart or scale. Autoscaling groups may launch dozens of new workers during heavy workloads, each with different outbound addresses. Suddenly, half the infrastructure falls outside the allowlist.
Automation Creating Constant IP Churn
Large scraping and monitoring systems launch new workers continuously. Old instances disappear while new ones appear with fresh network identities. Static allowlists struggle to keep pace with this level of automation.
Regional Routing Causing Unexpected Traffic Paths
Traffic does not always exit the network from the region engineers expect. ISP proxy networks rely on specific provider infrastructure, which means routing decisions can shift depending on ISP coverage. Allowlist rules based purely on geographic assumptions can break unexpectedly.
How Swiftproxy Handles Authentication and Access Control
Effective access control must match how real teams operate. Otherwise, security controls become fragile and frustrating.
Swiftproxy designed its authentication model with that reality in mind. Instead of forcing teams into rigid configurations, the platform offers several complementary ways to control proxy access.
Native IP Authorization
Swiftproxy ISP proxies support built-in IP authorization. That means you can restrict proxy access to approved source addresses without relying solely on usernames and passwords. Access becomes tied to your network architecture rather than scattered credentials across dozens of services.
IP Whitelisting for Proxy Endpoints
Whitelisting allows only trusted source addresses to connect to the proxy layer. Once your infrastructure uses stable egress IPs, proxy access becomes predictable and tightly controlled. Jobs can run anywhere internally while still respecting the security boundary.
User-Based Authentication
Different teams should never share the same credentials. Swiftproxy supports separate user accounts for different services and groups, making it easy to rotate credentials or revoke access without disrupting unrelated workflows.
Granular Exclusivity Levels
Swiftproxy ISP proxies are available in shared, private, and dedicated tiers. These exclusivity levels align well with least-privilege principles. Teams running sensitive workflows can isolate their traffic without paying for unnecessary resources.
Role-Based Access Control
Large organizations often maintain multiple proxy pools. Role-based access ensures that teams can only use the pools assigned to them. This prevents accidental cross-usage that leads to blocked traffic or unexpected billing spikes.
Detailed Activity Logs
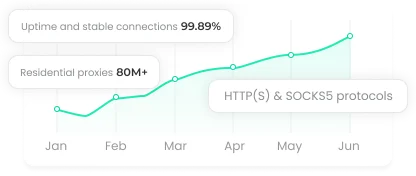
Visibility matters. Swiftproxy provides detailed logs showing how proxies are used, which endpoints are accessed, and where requests originate. With infrastructure reliability reaching 99.98 percent uptime, anomalies in those logs actually mean something instead of being lost in random system noise.
Keeping Whitelisting Secure Without Breaking Performance
Security controls often introduce friction. IP whitelisting does not have to. When implemented correctly, it strengthens infrastructure without slowing proxy workloads.
One advantage of ISP proxies is their static IP design. Because the proxy addresses do not rotate, allowlists remain stable over time. The same IP address approved today will still be valid months later. That dramatically reduces maintenance overhead compared with rotating proxy environments.
Regional targeting also remains clean. Instead of relying on username parameters or session configurations, ISP proxies route traffic through specific provider networks such as AT&T or Sprint. The allowlist controls where traffic enters the system, while the ISP layer determines geographic routing.
Automation benefits as well. As long as your workers send traffic through known egress points, you can scale infrastructure freely without constantly updating allowlists.
Finally, whitelisting naturally separates proxy traffic from internal networks. Requests originate from controlled exit points rather than directly from production systems, which limits exposure if something goes wrong.
Implementing IP Whitelisting
Implementing IP whitelisting does not require massive infrastructure changes. But it does require thoughtful planning.
Identify Which Services Actually Need Proxy Access
Start by mapping every job and service that communicates with proxies. Production scraping systems, scheduled monitoring tasks, and occasional research scripts all fall into this category. Knowing exactly who uses the proxies helps prevent overly broad access rules.
Create Stable Egress Points
Route outbound traffic through predictable network addresses. NAT gateways, fixed outbound IPs, or controlled network exits make whitelisting far easier to manage. Stability here eliminates most allowlist maintenance headaches.
Handle Remote Access Carefully
Home networks and shared Wi-Fi introduce unpredictable IP addresses. Instead of adding them directly to allowlists, route developer traffic through VPN gateways or jump hosts. This keeps access predictable even when engineers move between networks.
Combine Whitelisting with Authentication
IP restrictions control where traffic originates, but they do not identify who initiated it. Pair allowlists with individual user credentials so activity can always be traced back to a specific service or engineer.
Monitor Usage and Rotate Credentials Regularly
Access paths tend to linger long after they are needed. Review usage logs periodically and remove inactive endpoints. When rotating credentials, schedule changes carefully so active jobs do not fail mid-execution.
Where Strong Proxy Access Control Makes the Difference
Strict proxy access controls are not just about security policies. They also improve reliability and data quality in real operational workflows.
Ad verification teams rely on trustworthy traffic sources to confirm how advertisements appear across different locations. When proxy traffic originates from uncontrolled systems, results become inconsistent and harder to explain to advertising platforms.
Brand protection teams benefit as well. Monitoring domain spoofing or impersonation campaigns requires automated scans across thousands of websites. Restricting proxy access ensures those scans originate from predictable systems rather than internal environments that should remain isolated.
Competitive research workflows also gain protection. Routing these activities through ISP proxies prevents corporate networks from appearing in competitor server logs. At the same time, access restrictions limit who inside the organization can run those research tasks.
Threat intelligence pipelines may see the biggest benefit. Data collected through stable, controlled proxy environments produces far cleaner signals. When one source fails or becomes blocked, it can be replaced without contaminating the rest of the dataset.
Final Thoughts
By combining stable ISP proxies, precise IP whitelisting, and user-based controls, teams secure access without sacrificing performance. This ensures reliable data, protects internal networks, and strengthens workflows—from ad verification to threat intelligence—turning proxy management into both a security and operational advantage.