Top Proxy Providers for 2026 for Real Workloads
Proxy infrastructure is a core utility when real workloads depend on it. The right provider doesn't just deliver IPs—it reduces failed requests, stabilizes sessions across regions, and keeps your automation predictable as you scale. That's why we dug into the market and tested providers, so you can choose with confidence in 2026. This guide breaks down proxy types, performance signals, and pricing models. You'll learn how to compare vendors like a buyer, not a guesser.
What Changed from 2025 to 2026
Bot traffic has been rising steadily, and it's not slowing down. According to Imperva's 2025 Bad Bot Report, automated traffic climbed from 47.5% in 2022 to 51% in 2024, while bad bot traffic surged from 30.2% to 51% in 2024/2025. AI and LLM adoption is making automation cheaper and easier to scale, and platforms are responding with stricter scoring and tighter session scrutiny.
So if this trend continues into 2026, your proxy provider needs to do more than "just work." It needs to look legitimate to the platforms you target.
Here's what has changed for modern workflows:
Platforms now score traffic quality, not just IPs.
Your sessions must feel stable and human-like. A rotating proxy that changes too often is a red flag.
Residential and mobile pools are under heavier scrutiny.
Providers with weak sourcing get burned fast on sensitive targets. Security teams are using ML to detect abuse.
Geo targeting is now baseline functionality.
City, ASN, and ISP controls aren't "nice to have." They're table stakes for monitoring, QA, and multi-step flows.
Pricing models have become more engineering-shaped.
The real cost is not bandwidth—it's retries, concurrency, and geo premiums. You should compare providers by cost per successful request, not headline units.
Compliance and KYC now differentiate providers.
Some residential proxy suppliers still attract abuse-driven sources. Screening, transparency, and enforcement matter more than ever.
How to Match Proxy Providers to Your Workflow
Below, each workflow is matched with proxy types, session settings, and plan checks that matter most.
1. LLM and Data Enhancement
If your pipeline is feeding LLMs, stability matters more than raw speed. Residential pools give breadth, but ISP exits deliver repeatable sources. You should keep sessions sticky when pagination or chaining occurs. Concurrency should be conservative to reduce churn.
Detailed error breakdowns by domain and status code. You need it to optimize at scale. Also, avoid providers that hide throttling behind vague "fair use" terms. Look for API-based usage and limit tracking, so your pipeline doesn't fail silently.
2. Web Scraping and Competitive Insights
For scraping, your goal is predictable scaling and cost efficiency. Datacenter IPs are best for low-risk public pages. Use residential only when geo realism is necessary. Rotate by default for single-page requests, and switch to sticky sessions only when the flow needs state.
Retries are a pricing multiplier. So run a pilot, calculate cost per successful request, and lock in clear overage rules before you commit. That alone saves you from surprise bills and wasted effort.
3. Testing and Performance Tracking
Testing and monitoring are about repeatability. Not coverage. You want static exits per region and a small fixed egress set for clean baselines. Stability matters more than scale here.
Look for low jitter, stable routing, a public status page, and incident history. If the provider reshuffles exits mid-session, your results become meaningless. That's why session control is essential.
4. Ads and Accounts Management
For ads and accounts, consistency is the priority. Dedicated ISP or mobile exits often work best because they preserve identity signals. Geo consistency matters, and IP rotation must be controlled. Mid-session rotation is a fast track to account flags.
You also need strict access controls, auditable team seats, and allowlists or token auth. Shared exits are fine for scraping—but not for account work.
Types of Proxy
1. Datacenter Proxies
Fast, cheap, and scalable. Great for low-risk pages and monitoring. But platforms flag them quickly on consumer-facing sites.
2. Residential Proxies
Better geo realism and stronger "normal user" signals. Use them when targets react to datacenter traffic. They're slower and cost more, but they're the best baseline for coverage.
3. ISP Proxies
A middle ground. They provide stable, long sessions with fewer surprises. Ideal for multi-step flows and repeat checks.
4. Mobile Proxies
Carrier-like traffic with strong reputation. Expensive, limited throughput, and best used only when mobile reputation matters.
5. Shared vs Dedicated Proxies
Shared is cheaper but adds reputation noise. Dedicated costs more but protects stability for accounts and monitoring.
The 5 Popular Proxy Providers
Here's a shortlist of vendors that deliver geo targeting, stable sessions, and reliable protocol support. Use this as your starting point, then validate performance against your real targets.
1. Swiftproxy
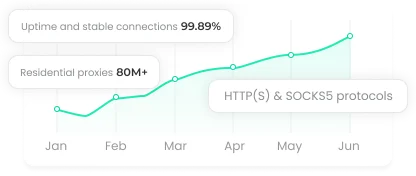
Swiftproxy is strong for fast rollout and clean setup. It supports ISP and residential proxies. The dashboard offers city/state targeting and flexible authentication. The API supports lifecycle automation, including renewals and usage tracking.
2. Proxy-Seller
Proxy-Seller is built around rotation and targeting. You can switch between time-based rotation, per-request rotation, and sticky sessions. It supports ISP-level targeting and offers a wide geographic footprint.
3. Bright Data
Bright Data combines a massive IP network with managed scraping tools. You can target by city, carrier, or ASN, then offload extraction and parsing to their APIs. This reduces retries and speeds up LLM enrichment pipelines.
4. Oxylabs
Oxylabs focuses on high-volume data collection and managed scraping. It offers Web Unblocker for tough targets and structured Scraper APIs that reduce parsing overhead. Their rate caps and uptime guarantees make planning easier.
5. Decodo
Decodo offers a large residential network with both rotating and sticky sessions. It includes API-based team tooling, sub-user limits, and usage monitoring. Their workflow tools are built for fast adoption.
Final Thoughts
In 2026, the right provider determines whether your automation stays stable, your data stays reliable, and your growth stays predictable. Platforms are stricter, so test providers against your real workflows. The best proxy won't just deliver IPs—it will keep your operations running smoothly as you scale.