Why Businesses Rely on Proxy Servers for Secure Network Control
More than 90% of cyberattacks start with a simple request. That single stat should make anyone pause. Because every click, every login, every page load is a request leaving your device and stepping into the unknown. That's exactly where proxy servers step in—and why they matter more than most people realize! A proxy server sits quietly between you and the internet. It intercepts your requests, forwards them, and returns the response as if nothing happened. Simple on the surface. Powerful underneath. You're no longer exposed directly, and that subtle shift changes everything about how your data moves and how secure it really is.
What a Proxy Server Does
Think of a proxy as your digital middleman—but one that works in your favor. You send a request. The proxy evaluates it, forwards it, and returns the response. Clean. Efficient. Controlled.
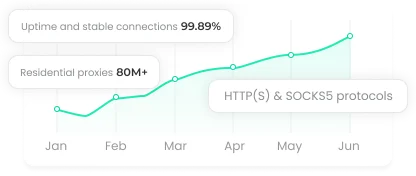
That control unlocks several advantages at once. You can filter content, monitor activity, and even speed things up through caching. Yes, faster performance and tighter security can coexist! And when your real IP address is hidden, you gain a level of privacy that's hard to achieve otherwise.
But here's where it gets interesting. Not all proxies behave the same way. Some prioritize transparency, others prioritize anonymity, and a few are built for high-performance environments where speed and reliability are non-negotiable.
How Proxy Servers Function
Every time you connect to a website, your IP address travels with your request. That's your identifier. Your footprint.
A proxy replaces that identifier before the request moves forward. The destination server only sees the proxy—not you. When the response comes back, the proxy passes it along. You get the content. The server never sees your real details.
Then there's caching. Frequently accessed data gets stored locally, reducing the need to fetch it repeatedly. That means faster load times and less strain on your network. It's one of those small features that delivers outsized impact when used correctly.
Why Proxy Servers Matter
Cyber threats aren't slowing down. They're scaling. A well-configured proxy acts as your first line of defense, blocking malicious traffic before it ever reaches your systems. It can enforce access policies, prevent risky behavior, and reduce exposure across the board. For businesses, this means fewer incidents. For individuals, it means fewer sleepless nights worrying about compromised data.
There's also a visibility angle that's often overlooked. With the right setup, you can track usage patterns, identify unusual activity, and respond before small issues become major problems. That's not just security—that's operational intelligence.
Privacy Protection
Your IP address says more about you than you think. Proxy servers replace your real IP with another one, making it significantly harder for websites, trackers, or attackers to pinpoint your identity. That alone is a major win. But combine it with encrypted connections, and you're adding real protection—not just surface-level masking.
This becomes critical on public networks. Coffee shops, airports, hotels—convenient, yes. Secure, not always. Routing traffic through a proxy adds a protective buffer that most users don't realize they're missing until it's too late.
And then there's access. Need to reach content restricted in your region? A proxy can route your traffic through another location, opening doors without compromising your security setup.
When to Use Proxies
In business environments, proxies are less about convenience and more about control. They regulate internet access, enforce company policies, and reduce bandwidth strain through caching. The result? A faster, safer, more predictable network.
They also play a key role in scaling operations. High-traffic environments rely on proxies to distribute load, manage incoming requests, and maintain uptime under pressure. When performance matters, proxies aren't just helpful—they're essential.
For individual users, the value is more personal but just as impactful. You get privacy, safer browsing, and more freedom online. Whether you're protecting sensitive information or simply avoiding unnecessary tracking, a proxy gives you back a level of control that most people unknowingly give away.
Choosing the Right Type of Proxy
Not all proxies are created equal—and picking the wrong one can undermine everything.
Transparent proxies are useful for monitoring and control, but they won't hide your identity. Forward proxies strike a balance between usability and security, making them a solid general-purpose choice. Anonymous and high-anonymity proxies go further, actively protecting your identity and making tracking extremely difficult.
Then there are residential proxies. These use real IP addresses tied to physical devices, which makes them far harder to detect and block. If reliability and stealth matter, this is often the direction professionals take.
Reverse proxies, on the other hand, protect servers instead of users. They manage incoming traffic, distribute load, and add a protective layer between external users and internal systems. Different role. Same importance.
The Risks You Can't Ignore
Let's not pretend proxies are foolproof. They aren't. Some providers log your data. That defeats the entire purpose of using a proxy for privacy. Others don't offer encryption, leaving your information exposed despite the added layer. Free proxies, in particular, often come with hidden trade-offs—slow speeds, unreliable connections, or worse, data harvesting.
The solution is simple, but often overlooked. Vet your provider. Read their policies. Test their performance. A proxy should reduce risk, not introduce new ones.
Final Thoughts
Proxy servers are not a silver b ullet, but they are a powerful layer of control in an increasingly exposed digital world. When chosen and configured carefully, they enhance privacy, improve performance, and strengthen security. The key is not just using proxies, but using them wisely and deliberately.