How Anti-Bot Systems Detect Automation and How to Avoid Detection
Websites have grown smarter. They’re constantly fighting off bots. Some are harmless—like search engine crawlers or security testers—but others can overload servers, steal data, or spam forms. Anti-bot systems exist to protect sites from these threats. But if your goal is legitimate automation, understanding these defenses is helpful.
How Anti-Bot Systems Identify Automated Activity
Anti-bot systems are detectives at heart. They monitor every visitor, gathering clues to spot behavior that doesn't fit a human pattern. Once a system flags a visitor as suspicious, it may block access or throw a CAPTCHA in the way.
These systems operate on three main levels including network, browser fingerprint, and user behavior.
1. Network Level
The network is the first line of defense. Anti-bot systems inspect IP addresses, request patterns, and packet headers. Certain IPs—like those from datacenters, Tor networks, or flagged blacklists—are scrutinized heavily. Ever solved a CAPTCHA just because you were on a VPN? That's network-level detection in action.
2. Browser Fingerprint Level
Every device leaves a unique footprint. Systems track browser type, version, language settings, screen resolution, fonts, hardware noise, media devices, and more. Collectively, these form a "browser fingerprint" that can identify a bot even if the IP looks normal.
3. Behavioral Level
Advanced systems don't stop at devices—they watch actions. How fast you scroll, how clicks are distributed, even how you move your mouse can reveal automation. Inconsistent or robotic patterns raise red flags.
Strategies for Bypassing Anti-Bot Systems
To bypass detection, you need to operate at all three levels simultaneously. There's no single trick—success requires a combination of masking techniques, high-quality tools, and precise execution.
1. Network-Level Hiding
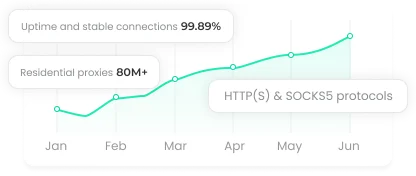
Your IP address acts as your identity online, and misuse can quickly lead to blocks. When sending large numbers of requests, high-quality residential or mobile proxies become important. Rotating proxies help distribute traffic across multiple IP addresses, reducing obvious patterns and making automated activity harder to detect.
When choosing proxies, check several key factors. Look at the IP reputation using tools like PixelScan or the iplists.firehol.org database. Test for DNS leaks with DNS Leak Test to ensure your real server is not exposed, and consider using ISP-owned proxies because they are usually less suspicious.
2. Browser Fingerprint Hiding
Anti-detect, multi-accounting browsers like Octo Browser are game changers. They allow you to spoof fingerprints at the kernel level, letting you run hundreds of browser profiles as if they were unique users.
You can automate these profiles using any browser automation library. Each profile can be set up with specific fingerprints, proxies, and cookies, ready for either manual or automated tasks. Professional anti-detect browsers also provide APIs with step-by-step guidance in multiple programming languages.
3. Simulating Real User Actions
Bots are not only detected through IP addresses or browser fingerprints. Many systems also analyze user behavior to identify automation. Real users rarely scroll at perfectly timed intervals, click links instantly, or complete forms at machine-like speed, so these patterns can quickly raise suspicion.
To avoid detection, actions should appear more natural and varied. Introducing irregular delays, randomizing mouse movements and keystrokes, and interacting with content in a realistic way can help. This may include scrolling through pages, clicking "Read more," submitting forms, or following links. Tools such as Selenium, MechanicalSoup, and Nightmare JS can help simulate these behaviors more effectively.
Conclusion
Automation works best when every layer moves in harmony. Network identity, browser fingerprint, and user behavior must all look natural and consistent. Ignore one layer and detection becomes far more likely. Treat anti-bot systems as sophisticated observers, and design your automation to blend in rather than stand out.